Our mission
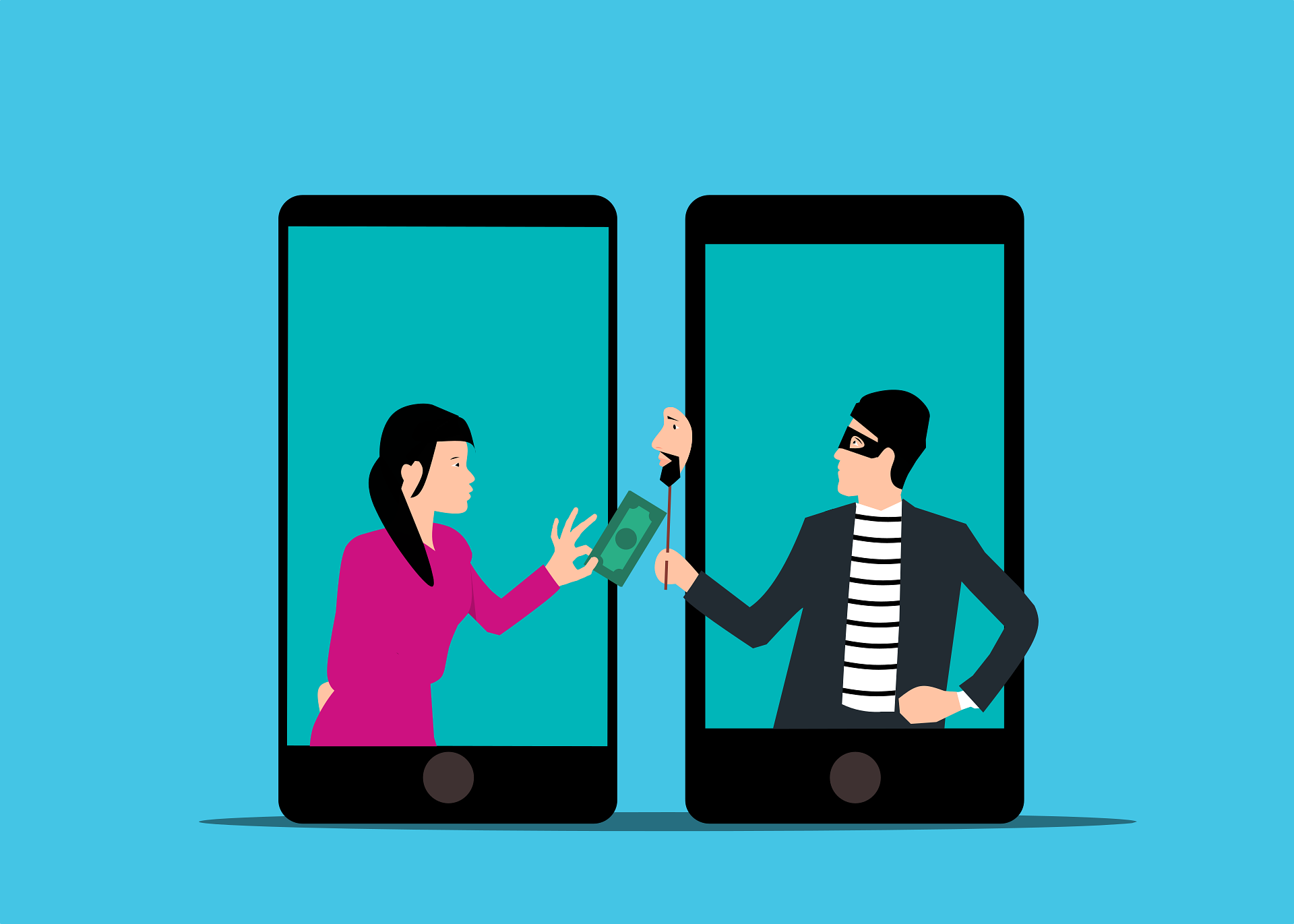
Metis - Prepare your next Phishing Awareness campaigns
Raise awareness among your employees with our SaaS solutions. Train your employees to recognize threats and report them.
Why choose Metis from Oletros?
Some points that led us to build this solution.
Real world techniques
We constantly track malicious actors, allowing us to be constantly informed of current techniques, from spoofing to QRishing.
Not only templates
We use Microsoft templates of course, but we are also able to use the forms of your solutions exposed on the Internet such as your SSO.
Threat evolution
Several difficulty levels available and the possibility of spreading out the campaign over time, all with the aim of avoiding the effect of campaign fatigue.
User segmentation
As some users are more sensitive than others, we have chosen to put a segmentation of your users in place and thus allow targeted campaigns.
Train users
Because prevention is nothing without improvement, we explain to trapped users how to detect phishing.
Real time metrics
You will have all the metrics in real time, as well as evolution graphs by user, segments and at the global level.
Use cases
Discover how Metis serves as the ideal platform, providing methods & training to improve the vigilance of your employees
Domain identity theft
Customer situation
With our EASM service, we had found unsecure domains on the client perimeter. This allowed an attacker to send emails pretending to be the company, and without the security systems blocking it because it was allowed by an overly flexible configuration. The poc that we presented was striking for them, even for internal cybersecurity team.
Our resolution
We made a report, explained how to resolve the incident and what technologies to rely on to facilitate the resolution. Then we proposed our platform to build targeted campaigns against IT people.
Phishing training
Customer situation
A company needed a guide to send to employees to understand the broad outlines of phishing and social engineering methods.
Our resolution
We have produced a guide in the form of a document with the different common attacks accompanied by video demonstrations on their perimeter. We contributed to the creation of a questionnaire to measure the uptake of information but also engagement around the subject.