· phishing · 4 min read
Open Redirect & Phishing
The purpose of this article is to highlight a basic method to bypass certain safety measures while deceiving the user. What could be better for phishing!
Short introduction to lay the foundations
Phishing, long neglected, now at the heart of everyone’s minds has been able to renew itself in recent years both on the attacker and defender side.
Methods are evolving rapidly, as defensive tools. In recent years, we have seen solutions move from a classic Bayesian filter to so-called artificial intelligence solutions, without the changes being massive in terms of detection. The charge for the blueteam in terms of phishing has exploded year after year
I will present here a rather unknown but simple and particularly effective method against security systems based on the “quality” of the domain & on known threats through Open Databases. Quality is measured by calculating domain age, domain authority and so on.
But what is the Open Redirect?
The Open Redirect, we often encounter it when we talk about the Web Exploitation, during an audit or a pentest. Very often, it is caused by a lack of sanitization so it often happens that the same parameter in question is vulnerable to a Cross Site Scripting, Local File Inclusion, Remote File Inclusion or even a XML External Entity.
Often considered a minor problem in terms of pure security, the last few years have shown that it can be a major problem in terms of seo and phishing.
Let’s skip the SEO part for this article even if there is a lot to say and let’s focus on the case of phishing.
I’ll give you a simple definition:
An Open Redirect is an unwanted redirection, without user interaction, from site A to site B.
And because nothing beats an example, I’ll give you an Open Redirect that I found recently:
Thanks to the Direction Generale de l’Aviation Civile for his involuntary collaboration with my article
PS: Well done for having patched this quickly :)
So if you take this link, and click on it, you will be redirected to the google site without your consent, when you were supposed to click on a civil aviation link. That’s an OR.
Now the concrete.. Open Redirect & Phishing
I think you should see right now where I’m coming from. With an OR, with site A a respectable, credible site with real activity and site B a malicious, recent website, clearly phishing, we can arrive to escape defensive service.
If, for example, you were thinking of implementing a domain age system to combat spam and phishing, know that you should also check the method. Indeed, if you classically retrieve the value of the domain in an OR case, the extracted domain will be domain A and not malicious domain B.
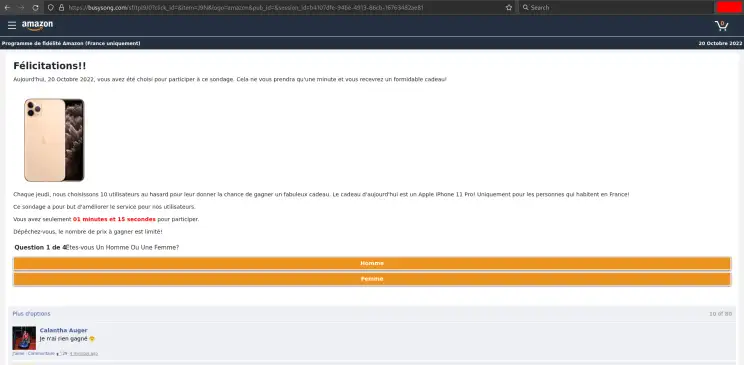
A little practice now. This time, I suggest you take another example than the one above with a real phishing page. And I will use an ongoing campaign to be in real condition. Here is the phishing page once you are on it:
So we can clearly see that it’s a phishing page, in the colors of Amazon because I chose Amazon via the GET logo parameter. This campaign does not only target Amazon but also french companies.
For security reasons, I will put the malicious URL in code tags. The url of the page is therefore:
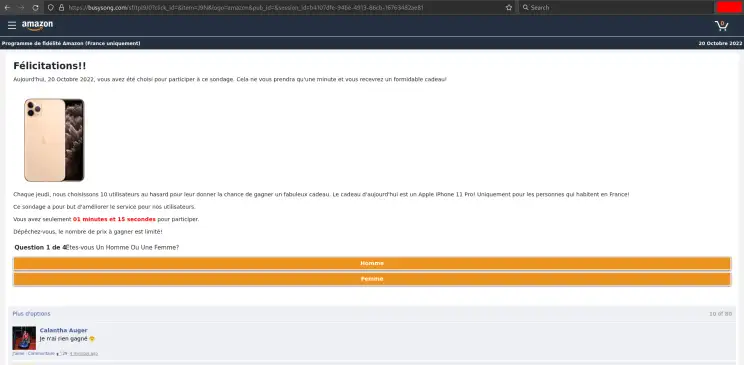
https://busysong.com/sf/tpl9/0?click_id=&item=J9N&logo=amazon&pub_id=&session_id=Of course I tested it on urlscan.io: https://urlscan.io/result/6a9a7105-f7c2-4252-887b-9aff3bdca7f6/
And on https://www.isitphishing.ai from Vade:
This is not yet detected by this solution but the overall idea is made. So we have an obvious phishing page with a bad domain.
Now let’s take an OR used by an ongoing phishing campaign, and use the phishing URL given above:
http://social.bigpress.net/api/emailtrack/click?goto=https://busysong.com/sf/tpl9/0?click_id=&item=J9N&logo=amazon&pub_id=&session_id=You will see the redirect!
To finalize the demonstration, I offer you a small experiment using the urllib library to retrieve the domain value: 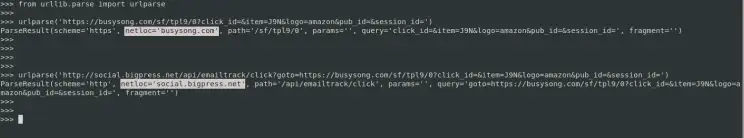
These 2 links both point to the phishing page but in the 2nd case, the OR causes the parsing to consider the domain of the url as being bigpress one and not the destination domain which is buysong.
Of course, it is possible to further improve this method, by combining it with other methods, or by disguising the link in an html tag.
Have fun and happy phishing everyone ;)